What Is Domain Spoofing? (+ How It Hurts Your Brand)
TL;DR: Domain spoofing is a significant threat in online advertising, leading to substantial revenue loss by displaying ads on fraudulent sites under the guise of reputable ones.
- Definition: Domain spoofing occurs when ads are set to appear on a specific, reputable domain but are instead shown on a less reputable or entirely different site.
- Impact: Can drain advertising budgets, damage brand reputation, and undermine consumer trust.
- Detection and Prevention: Recognizing signs like mismatched traffic quality and suspicious publisher behavior is key. Employing ad fraud solutions, verifying publisher credibility, and using white-listing can prevent spoofing.
- Consequences: Besides financial losses, it poses severe risks to brand safety and SEO optimization.
Domain spoofing can cost advertisers up to $1 million in lost revenue per month.
It’s something you usually don’t know is going on, until your budget runs out with no return for your campaign. While the term “spoofing” is commonly associated with email domain spoofing and phishing campaigns, URL spoofing is a threat specific to companies engaging in online advertising.
How do you define domain spoofing as it relates to online advertising? What’s the impact of spoofing on companies looking to advertise online? How can you spot domain spoofing ad fraud and thwart it?
We’re here to help you learn how to prevent becoming a victim of this costly scheme.
Defining Domain Spoofing
Ad fraud, as a whole, is complex. That’s why it’s important to break down the methods fraudsters use to better protect your brand.
We define domain spoofing as: When a publisher declares in the real-time bidding (RTB) that an ad will run on a specific domain, but is actually set to appear on a different, less favorable website. Fraudsters try to profit from the domains of reputable publishers, so what you see isn’t always what you get.
How Does Domain Spoofing Work?
Like with most types of ad fraud, domain spoofing attacks aim to “earn” fraudsters money while draining your brand’s advertising budget.
Domain spoofing for ad fraud involves hiding the actual domain of a website from the viewer. On the surface, the URL will look like it hosts a reputable site, but it’s really a trick (i.e., a “spoof”). So, while you think you’re bidding on a reputable website, your ad will show up someplace much different.
A fake URL might be extremely subtle, like ABCCompany1.com when the real company’s website is ABCCompany.com.
If a fraudulent publisher is spoofing their domain, it’s probably not the cleanest site. If the ad appears next to inappropriate or controversial material, it can create some major brand safety issues. For example, imagine if a Warner Bros ad was running on an illegal streaming site.
Domain spoofing isn’t necessarily fraudulent traffic, because the person on the other end may be real, but your ad is being shown on a different site (and to a different audience) than what you originally bid for. You’re essentially wasting your hard-earned advertising dollars on ad placements that won’t result in quality traffic.
Learn More about the Rise of Affiliate Marketing Fraud: Download the Whitepaper
Domain Spoofing Signs to Look Out For
You might be a victim of domain spoofing if you see any of these five signs.
- The domain traffic quality doesn't add up.
- The CPM (cost per mille, or every thousand impressions) is too good to be true.
- The domain has no ads.
- The publishers don’t sell ad space in RTB auctions.
- You notice a suspicious email address (like the one pictured below).
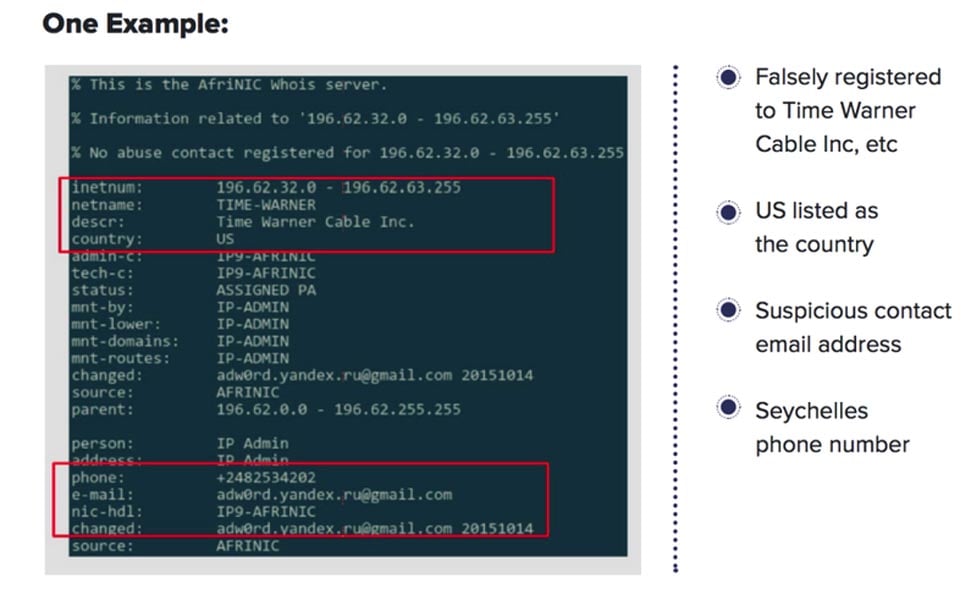
Source: Forbes
Website vs. Email Spoofing (AKA URL Spoofing vs. Phishing)
The term “domain spoofing” may spark some confusion since it is commonly associated with email spoofing instead of website spoofing. The primary difference between email domain spoofing and website spoofing is what is being spoofed.
In website domain name spoofing, the information being faked is the URL of the website. URL spoofers commonly try to pass off one website as another. Entire fake websites might be created as part of a website spoofing campaign.
In email domain name spoofing, on the other hand, malicious actors are typically trying to trick someone into thinking that a specific email came from a different domain or account than the sender’s actual email.
For example, a spoofed email sender address might read like it’s from a trusted source such as user.name@reputablebusiness.com instead of scammer@pirates.org.
The sender’s email may also have a spelling error or added character that is easy to miss, making it seem like it’s a legitimate message. That’s why it’s important for businesses to spot the signs of phishing attempts to stop these fraudulent emails from leading to a larger data breach.
To summarize, where website URL spoofing seeks to trick businesses into falling for ad fraud, phishing attacks use email domain spoofing to make their targets take a variety of actions (such as approving fake invoices, surrendering user login or account details, or downloading malware) as part of a larger fraud campaign or cyberattack.
How Domain Spoofing Hurts Your Brand
You can now see how domain spoofing differs from traditional ad fraud that involves fraudulent traffic. But that doesn’t mean it isn’t hurting your brand. If you’ve been defrauded, your campaign won’t be optimized for search engines. This ultimately hurts your SEO.
Related Post: How Ad Fraud Affects Your Brand Safety
And besides the aforementioned brand safety issues, domain spoofing can potentially hurt you by lowering consumer trust and draining your ad budget. You won’t want a potential customer seeing your ad next to any sketchy material. And remember: Because there's no legislation on ad fraud, fraudsters get to pocket what they steal.
Fake domains may seem harmless, until your ads show up alongside unsavory materials and you start to see your advertising dollars drain away.
Domain spoofing is more damaging than just a few lost impressions; if you’re a victim of domain spoofing, your reputation is on the line.
And as Warren Buffett famously said: “It takes 20 years to build a reputation and five minutes to ruin it. If you think about that, you’ll do things differently.” Restoring your brand’s reputation is possible, but can take years of work and resources to regain a positive image and consumer trust.
How to Stop Domain Spoofing
Luckily, there are a few ways you can prevent domain spoofing from impacting your brand. Fraudsters can create fake website fairly easily, so it’s important to have a keen eye to spot fake sites from legitimate sources.
Here are some tips to help stop domain spoofing ad fraud.
1. Always Check Your Work
When bidding for ad placement, make sure you know your publisher. Ask for transparency and check to make sure they are who they say they are.
2. Avoid Blacklisted Publishers
This might seem obvious, but fraud can sometimes be difficult to spot. Stick to what you know and avoid any questionable publishers.
Related Post: What You Need to Know About ads.txt
3. Get a Third Party to Double Check
A third-party perspective can be a game changer when looking at data. Someone else might be able to see what you can’t.
4. Get Protected
Ad fraud solutions are no longer a want, but a need. Investing in an ad fraud solution can help you identify domain spoofing before it can hurt your campaign.
Falling victim to domain spoofing can have a lasting impact on your brand, resulting in lost revenue and decreased brand safety and consumer trust. While domain spoofing can be hard to spot, knowing the signs and risks can help you to proactively defend your brand against fraudsters.
Learn more about how Anura can help protect your brand from domain spoofing. Sign up for a free trial today.
FAQs about Domain Spoofing
Have more questions about domain spoofing? Take a look at some of the most common questions about this type of fraud.
What Are the Different Types of Domain Spoofing?
There are several distinct types of domain spoofing, including:
- URL/Website Spoofing: When a website’s URL is disguised as something else – usually to make a fraudulent website look like a more reputable one.
- Email Domain Name Spoofing: When an email’s domain name is faked to make the email look like it is coming from a trustworthy source – often used in phishing campaigns.
- Caller ID Spoofing: When someone makes their phone number look like a different phone number during calls. Often used to get around Caller ID blocks or to trick people into answering calls they’d otherwise ignore.
- IP Spoofing: When someone hides their computer’s internet protocol (IP) address online to impersonate other users or hide their identity online.
- Browser Spoofing: When one web browser spoofs the user agent string of a different type of browser (Chrome, Firefox, Edge, etc.). This may result in some web pages not displaying correctly, as some sites use specialized rendering for different browsers. Also known as user agent spoofing.
How Do Fraudsters Use Spoofed URLs Against Companies?
There are a few different tactics that fraudsters can use URL spoofing for. One fraud strategy is to sell advertising space on websites that the fraudster doesn’t own. So, the business thinks it’s getting a great deal on advertising space on reallypopularwebsite.com, but is really getting ads shown on some dark website that won’t generate results (and may harm the brand by association).
Another way fraudsters can use URL spoofing is to trick people surfing the web into visiting a fake website that is designed to upload malware or trick the visitor into trying to “sign in” to their account with the legitimate website.
What’s a URL Shortener?
A URL shortener is a solution for taking a really long webpage URL and shrinking it down to something really short. If you’ve seen a bit.ly link, you’ve seen a URL shortener.
There is a legitimate use for URL shorteners, since they can help make links fit more easily into messages where character counts are limited (such as a text or tweet). However, some malicious actors use URL shorteners to disguise their spoofed websites in communications such as emails or social media messages.
How Do Fraudsters Spoof an Existing Website URL?
In URL spoofing, fraudsters often do something very minor to change the URL of a specific website to make it just different enough that they can claim the domain and set up their fake webpage.
A fake URL example could be something like Arnazon.com instead of Amazon.com – the lowercase “rn” looks like an “m” at a glance and could trick a reader in an email. Others might swap out letters or numbers in a domain name for non-Latin characters that look the same, but aren’t.
How Can I Spot a Spoofed Domain in My Ad Campaigns?
Keep an eye out for warning signs like ridiculously low CPM prices, publishers not selling ad space in RTB auctions, ads getting suspiciously low clicks on what should be a high-traffic domain, and suspicious email addresses being used for the publisher’s emails.
If you suspect a domain is spoofed, pause any suspected ad placements and report the issue to your ad network or ad fraud solution partner. Together you can investigate the source of the traffic.
How Can Ad Fraud Solutions Protect Against Domain Spoofing?
Ad fraud solutions detect domain spoofing by analyzing discrepancies in traffic sources, employing sophisticated pattern recognition algorithms to identify unnatural behaviors, and comparing site metrics against known benchmarks.
In addition to these tools, implementing strict domain verification protocols, preferring to work with well-established ad networks, and using white-listing techniques to approve sites beforehand can also significantly reduce the risk of domain spoofing affecting your campaign.
Implement the world's most accurate ad fraud solution for your organization.


